In the current landscape of cloud-native computing, simply keeping a cluster running is no longer the definition of success. After witnessing the evolution of infrastructure from isolated hardware to fluid, automated containers, I’ve seen that security is the only thing that separates a high-performing system from a headline-making data breach. The Certified Kubernetes Security Specialist (CKS) is not just a badge; it is a professional statement that you understand the high-stakes environment of modern production systems.
What is the CKS Certification?
The CKS is a performance-based exam designed to validate an individual’s ability to secure container-based applications and the Kubernetes platform across the entire lifecycle—build, deployment, and runtime. Unlike many theoretical exams, this is a hands-on challenge that requires solving real-world security vulnerabilities in a live, timed environment. It stands as one of the most respected credentials for anyone aiming to reach the top tier of the cloud security hierarchy.
Who Should Take It?
This program is specifically tailored for experienced professionals who are already comfortable with the administrative side of Kubernetes but want to master the defensive side. It is perfect for System Administrators who are transitioning into DevSecOps, SREs who need to ensure platform resilience, and Security Engineers who want to understand the inner workings of container orchestration. If you are responsible for maintaining clusters that handle sensitive data or public-facing traffic, this is your mandatory next step.
Skills You’ll Gain
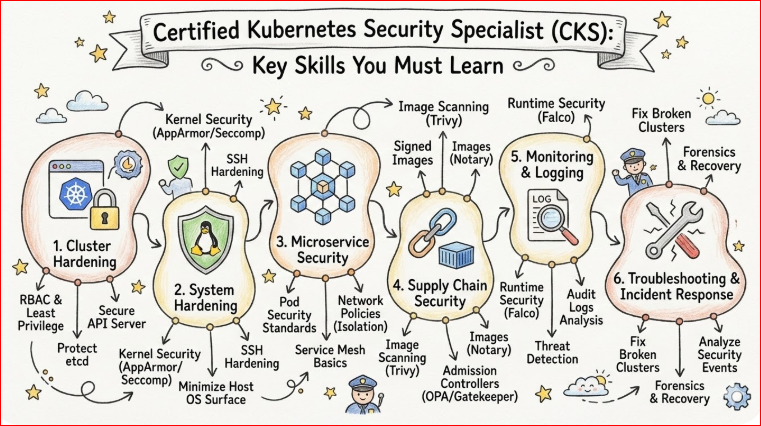
- Cluster Hardening: You will learn how to restrict access to the API server and use Kube-bench to ensure your configuration aligns with the CIS (Center for Internet Security) benchmarks. This is critical for preventing unauthorized users from gaining control of your infrastructure.
- System Hardening: Mastering the art of reducing the host’s attack surface by using kernel-level security features like AppArmor and Seccomp. This ensures that even if a container is compromised, the damage is contained and cannot spread to the underlying operating system.
- Supply Chain Security: You will gain the ability to verify the integrity of your software by scanning container images for vulnerabilities and signing them to ensure only trusted code runs in your environment. This stops “poisoned” images from entering your production pipeline.
- Monitoring and Logging: This skill allows you to implement tools like Falco to detect suspicious activities at runtime, such as an unexpected shell opening inside a pod. Being able to audit and respond to these events in real-time is what separates a reactive engineer from a proactive one.
Real-World Projects You’ll Be Able to Do
- Zero-Trust Networking: You will be able to design and implement a zero-trust network model using Kubernetes Network Policies to isolate microservices from each other. This ensures that a breach in one service does not lead to lateral movement across the entire cluster.
- Automated Security Pipelines: You can build automated CI/CD pipelines that automatically reject deployments if their container images contain critical vulnerabilities. This shifts security to the “left,” catching issues early in the development process before they ever reach a user.
- Intrusion Detection Systems: You will have the expertise to configure runtime security tools that monitor for anomalous behavior and send alerts to your SRE team immediately. This creates a resilient environment where threats are neutralized before they can do significant damage.
- Audit Logging and Remediation: You will be capable of setting up comprehensive audit logging for the Kubernetes API server to track every action taken within the cluster. This is essential for both compliance and forensic investigations after a security incident occurs.
Preparation Plans
7–14 Days (The Expert Sprint)
This plan is for those who are already living and breathing Kubernetes and have a recently cleared CKA. Spend these two weeks focusing exclusively on the specific tools like Trivy and Falco, and practice navigating the official documentation at high speed. You should be running at least two mock exams a day to build the muscle memory required for the performance-based tasks.
30 Days (The Professional Standard)
Spend the first two weeks deep-diving into the theory of system hardening and supply chain security. Use the remaining two weeks to build a local lab environment where you manually implement Network Policies and RBAC for complex, multi-namespace applications. This timeline balances theoretical understanding with the repetitive practice needed to master the command line.
60 Days (The Career Foundation)
In the first month, focus on the underlying Linux concepts, such as how namespaces and cgroups provide isolation at the OS level. During the second month, move into the Kubernetes-specific domains, spending ample time on each tool mentioned in the syllabus. This slow and steady approach ensures that you don’t just pass the exam, but actually retain the skills for your daily job.
Common Mistakes to Avoid
- Neglecting the Basics: Many candidates fail because they focus on advanced security tools but forget how to fix a basic configuration error in a Pod or Service. Ensure your foundational CKA knowledge is rock-solid before you attempt the specialized security tasks.
- Poor Time Management: The CKS is notorious for its strict time limit, and many engineers get stuck on a single difficult question. You must learn to skip a task if it’s taking too long and come back to it later, as every point counts toward your final score.
- Over-reliance on Memorization: Since this is a practical exam, memorizing answers will not help you when the environment changes. You must understand the underlying logic of why a configuration works so you can adapt to the specific scenario presented in the exam terminal.
- Ignoring Documentation Search: You are allowed to use official documentation, but if you don’t know the exact keywords to search for, you will waste precious minutes. Practice finding specific YAML examples in the docs so you can copy and paste them quickly during the test.
Choose Your Path: 6 Learning Tracks
| Track | Focus | Role of CKS |
| DevOps | Automation & Delivery | Ensures that every automated deployment is built on a secure foundation, preventing the automation of vulnerabilities. |
| DevSecOps | Security Integration | This is the flagship certification for this path, proving you can bake security into every stage of the lifecycle. |
| SRE | Reliability & Scalability | Focuses on preventing resource exhaustion and malicious attacks that could lead to system downtime or performance degradation. |
| AIOps/MLOps | AI Infrastructure | Secures the massive datasets and complex model-serving endpoints that are increasingly being hosted on Kubernetes clusters. |
| DataOps | Data Privacy | Crucial for engineers managing databases in containers, ensuring that persistent volumes are encrypted and access is strictly controlled. |
| FinOps | Cost Optimization | Helps prevent unauthorized resource usage, such as crypto-jacking, which can lead to unexpected and massive cloud bills. |
Role → Recommended Certifications
| Role | Primary Recommendation | Secondary Focus |
| DevOps Engineer | CKA + CKS | Focus on Jenkins or GitLab certifications to secure the CI/CD pipeline from end to end. |
| SRE | CKA + CKS | Add Prometheus and Grafana certifications to monitor for security-related performance anomalies in real-time. |
| Platform Engineer | CKS + Terraform | Combine cluster security with Infrastructure as Code (IaC) to ensure your cloud resources are “secure by design.” |
| Cloud Engineer | CKA + CKS | Gain a deep understanding of cloud provider-specific security tools like AWS KMS or Azure Key Vault to complement Kubernetes. |
| Security Engineer | CKS + CISSP | Bridge the gap between traditional enterprise security and modern cloud-native practices for a holistic defense strategy. |
| Data Engineer | CKA + Data Certs | Use CKS knowledge to protect the data pipelines and storage layers that sit on top of your container platform. |
| FinOps Practitioner | FinOps Certified | Use Kubernetes resource quotas and security policies to enforce cost-saving measures across multiple engineering teams. |
| Engineering Manager | KCNA + CKS | While you may not be “hands-on” every day, understanding these concepts allows you to lead security-first engineering cultures. |
Master Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Security | Specialist | Engineers/Admins | CKA | Hardening, Runtime, Supply Chain | After CKA |
| Administration | Professional | SREs/DevOps | Basic Linux | Cluster Mgmt, Troubleshooting | Before CKS |
| Developer | Professional | App Developers | Basic K8s | Pod Design, ConfigMaps, Secrets | Optional |
Where to Get Trained?
- DevOpsSchool As a pioneer in DevOps training in India and globally, DevOpsSchool offers a comprehensive CKS program that focuses on the practical application of security tools like Falco and Trivy. Their training is led by industry veterans and includes access to specialized lab environments designed to mirror the actual performance-based exam. It is highly recommended for engineers looking for deep-dive, instructor-led sessions with a focus on real-world scenarios.
- Cotocus Cotocus is recognized for its boutique and personalized approach to high-end technical training, specifically within the DevSecOps domain. Their CKS curriculum is designed to bridge the gap between container orchestration and cybersecurity, offering one-on-one mentorship that helps students understand the “why” behind security configurations. This institution is ideal for professionals who prefer a more interactive and tailored learning experience.
- Scmgalaxy Scmgalaxy serves as a massive community-driven hub that provides an extensive repository of resources, tutorials, and practice guides for the CKS exam. Beyond traditional training, it offers a platform for collaborative learning where professionals can stay updated on the latest Kubernetes security threats and remediation techniques. It is an excellent choice for self-starters who want a mix of structured content and community support.
- BestDevOps BestDevOps focuses on operational excellence, providing specialized CKS training that is heavily weighted toward runtime security and high-compliance environment management. Their courses are designed for engineers working in sensitive sectors like finance and healthcare, emphasizing the implementation of “defense-in-depth” architectures. They are known for their practical labs that focus on threat detection and automated auditing.
- DevSecOpsSchool.com This institution focuses specifically on the intersection of development, security, and operations, making it a natural fit for CKS preparation. Their program covers the entire software supply chain, ensuring students can secure not just the cluster, but the code and the pipeline as well. It is a top choice for those aiming for a dedicated career path as a DevSecOps Engineer.
- SRESchool.com SRESchool approaches Kubernetes security through the lens of system reliability and availability, teaching students how security breaches impact performance. Their CKS training includes unique modules on resource quotas and network policies to prevent resource hijacking and DDoS attacks. This is the preferred destination for Site Reliability Engineers who want to add security to their operational toolkit.
- AIOpsSchool.com AIOpsSchool provides a unique perspective on the CKS by focusing on the security of AI and Machine Learning workloads running on Kubernetes. Their training addresses the specific challenges of securing large-scale data processing and model-serving endpoints against modern threats. It is perfect for MLOps engineers who need to ensure their AI infrastructure is hardened against attacks.
- DataOpsSchool.com DataOpsSchool specializes in the security of data-intensive applications, focusing heavily on persistent volume encryption and secure data access within Kubernetes. Their CKS program is tailored for Data Engineers and Database Administrators who need to manage sensitive data in a containerized environment. This institution ensures that data privacy and integrity are at the forefront of your security strategy.
- FinOpsSchool.com FinOpsSchool highlights the critical link between security and cost management, showing how security misconfigurations can lead to massive cloud bills. Their CKS training includes modules on preventing unauthorized resource usage, such as crypto-mining, by implementing strict security controls. This is ideal for FinOps practitioners who want to use security policies as a tool for financial governance.
FAQs (General)
1. How difficult is the CKS compared to CKA?
The CKS is widely considered a major step up in difficulty because it requires a deeper understanding of external security tools and the Linux kernel. While the CKA tests if you can build a house, the CKS tests if you can make it bulletproof.
2. How long does the CKS certification last?
The certification is valid for 2 years, reflecting the rapid pace of change in the Kubernetes security landscape. This ensures that certified professionals are always up to date with the latest threat vectors and defensive tools.
3. Do I need to be a security expert to pass?
You don’t need a background in cybersecurity, but you do need to understand security fundamentals like encryption, least privilege, and network isolation. The course will teach you the specific implementation of these concepts within Kubernetes.
4. Is the CKA a strict prerequisite?
Yes, you must have an active CKA certification before you can take the CKS exam. The CKA provides the essential administrative foundation that the CKS builds upon.
5. How much time should I dedicate daily to preparation?
Consistency is key; dedicating 2-3 hours a day is much more effective than cramming for 10 hours once a week. This regular practice helps build the muscle memory needed to handle the command line under exam pressure.
6. Can I use the documentation during the exam?
Yes, you can use the official Kubernetes documentation as well as the docs for allowed tools like Falco and Trivy. Knowing how to navigate these resources quickly is a core part of the exam strategy.
7. Is the exam multiple-choice?
No, it is entirely performance-based, meaning you will be working in a real terminal on actual clusters. You will be graded on the final state of the system after you complete your security tasks.
8. What is the passing score?
The passing score is typically 67%, which allows some room for error, but given the time constraints, you need to be very precise. Every minor mistake in YAML syntax can cost you valuable points.
9. Will this help me get a job in India?
The Indian tech market is shifting heavily toward cloud-native and “secure-by-default” engineering, making the CKS a highly sought-after credential. Companies from Bangalore to Gurgaon are actively looking for certified specialists to secure their infrastructure.
10. What is the career outcome of getting a CKS?
Professionals with a CKS often see a significant jump in salary and are eligible for high-level roles like DevSecOps Lead or Cloud Security Architect. It is a powerful differentiator in a crowded job market.
11. Can I retake the exam if I fail?
Most exam vouchers include one free retake, which takes the pressure off your first attempt. Use the first attempt to understand the exam’s flow and identify your weak areas.
12. Which Kubernetes version is used in the exam?
The exam version is updated regularly to stay within one or two releases of the current stable Kubernetes version. Always check the official site for the specific version being tested during your window.
CKS Specific FAQs
- Which security tools are covered in CKS? The core tools include Trivy for image scanning, Falco for runtime security, and Kube-bench for configuration auditing.
- Do I need to learn OPA (Open Policy Agent)? While OPA is popular, the CKS focuses more on native Admission Controllers and basic policy enforcement.
- Is image signing part of the exam? Yes, understanding how to verify and sign images to ensure supply chain integrity is a key exam domain.
- How important is RBAC? RBAC is foundational; you will likely need to troubleshoot and refine complex permission sets to ensure least-privilege access.
- What is the most time-consuming part of the exam? Configuring Network Policies and debugging Falco rules usually take the most time due to their precise syntax requirements.
- Should I learn gVisor or Kata Containers? You should understand the role of container sandboxing and how to configure different runtime classes within a cluster.
- Is secret management covered? Yes, the exam covers how to encrypt secrets at rest and how to manage them securely within your pods.
- What’s the best way to handle the time limit? Practice using
kubectlaliases and imperative commands to generate YAML templates quickly instead of writing them from scratch.
Testimonials
“After years in the industry, the CKS was the first certification that actually challenged my practical skills. It forced me to rethink how I approach cluster architecture from the ground up.”
— Arjun M., Senior DevOps Engineer
“The training I received was instrumental in helping me bridge the gap between traditional IT security and the world of containers. I now feel confident leading my team’s DevSecOps initiatives.”
— Sarah L., Cloud Security Architect
Next Certifications to Take
- Same Track (Specialization): Pursue the Certified Kubernetes Cloud Native Associate (KCNA) if you want to broaden your understanding of the entire CNCF ecosystem beyond just security.
- Cross-Track (Expansion): Consider the HashiCorp Certified: Terraform Associate to master Infrastructure as Code, ensuring your security policies are automated and reproducible.
- Leadership (Management): If you are aiming for a Director or CISO role, the CISSP (Certified Information Systems Security Professional) is the industry standard for high-level security management.
Conclusion
The journey to becoming a Certified Kubernetes Security Specialist is a demanding one, but it is undoubtedly one of the most rewarding paths in modern technology. By mastering the art of securing clusters, you aren’t just protecting data; you are ensuring the stability and future of the digital world. This certification serves as a testament to your technical depth, your attention to detail, and your commitment to professional excellence. Take the first step today, invest in the right training, and join the elite group of engineers who keep the cloud safe.