Introduction
DevSecOps is not a toolset. It is a working style where security becomes part of daily delivery, not a late-stage audit. In real teams, security issues usually happen because of speed: fast releases, many dependencies, shared cloud accounts, and repeated copy-paste configs. DevSecOps fixes that by pushing security checks and guardrails into the same flow where code is built, tested, released, and monitored.
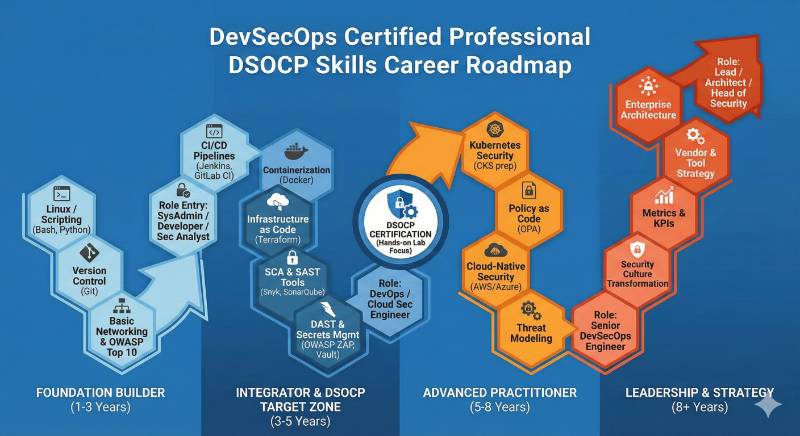
DevSecOps Certified Professional (DSOCP) is meant for engineers and managers who want to understand and apply DevSecOps in a practical way: secure CI/CD, safe infrastructure changes, secrets control, vulnerability triage, and secure cloud-native delivery.
This master guide expands every key point you need: what DSOCP is, who should take it, skills you will gain, real projects you should be able to deliver, preparation plans (7–14/30/60 days), common mistakes, and what to learn next.
Official reference page used for the learning ecosystem and track direction: DevSecOps Certified Professional (DSOCP)
Provider reference: Devopsschool
What is DevSecOps Certified Professional (DSOCP)?
DSOCP is a DevSecOps training + certification program focused on building secure software delivery practices. It teaches you how to integrate security into DevOps workflows so that security becomes continuous, measurable, and mostly automated.
Instead of treating security as a separate stage (after development), DevSecOps makes security a shared responsibility across development, operations, and security teams—supported by consistent pipelines and repeatable guardrails.
What DSOCP is really trying to help you do
- Release software faster without increasing risk.
- Catch issues early (in code review and build stages), not after production release.
- Build security controls that are practical: they block truly dangerous changes, and they reduce noise for the rest.
- Create a security culture where engineers do not fear security reviews, because the pipeline itself guides safe delivery.
Why DSOCP matters for working engineers and managers
Why it matters for engineers
Modern engineering work is rarely “just coding.” Most roles involve:
- Deployments and rollbacks
- Working with cloud services and access controls
- Handling secrets (tokens, API keys, certificates)
- Using containers and dependencies you did not write
DSOCP matters because it teaches you how to make these everyday actions safe and repeatable. When you implement DevSecOps well, you reduce:
- hotfix releases caused by security defects
- late-stage security rework
- production incidents caused by misconfigurations
- hidden risk from third-party dependencies
Why it matters for managers and leaders
Managers are responsible for delivery outcomes and business risk. DSOCP helps managers:
- set clear security expectations without slowing teams down
- define what must be blocked vs what can be warned
- create shared engineering standards (pipeline templates, policies, release checklists)
- improve audit readiness through consistency and evidence
The goal is not “more security tools.” The goal is safe delivery that scales.
Who should take DSOCP?
Software Engineers
If you are a developer shipping features, you benefit because:
- you learn secure coding habits aligned with real pipelines
- you learn how security issues appear in build logs, dependency reports, and container scans
- you become more confident in production changes
DevOps / Platform Engineers
If you own CI/CD and runtime infrastructure, you benefit because:
- you learn where to place security gates so they are effective, not annoying
- you learn secrets hygiene and access control patterns
- you learn how to standardize secure delivery across teams
SRE / Reliability Engineers
If you own uptime and incident response, you benefit because:
- many incidents are rooted in unsafe changes or risky configurations
- secure deployment practices reduce rollback frequency and outage risk
- better observability plus security signals improves response quality
Security Engineers working with product teams
If you support engineering teams, you benefit because:
- you learn how to push controls into developer workflows
- you learn practical vulnerability lifecycle management
- you learn how to reduce security friction by using automation
Engineering Managers
If you lead teams, you benefit because:
- you learn how to guide behavior through guardrails and standards
- you learn how to measure progress and outcomes
- you learn how to create adoption without creating fear or bottlenecks
Skills you’ll gain in DSOCP
1) Secure SDLC thinking
You learn where security fits in each phase:
- requirements and threat thinking
- design review (basic attack surface view)
- coding and code review
- build and test pipelines
- release and deployment
- monitoring and incident response
This changes security from a “final check” into a habit.
2) Secure CI/CD design
You learn to design pipelines that do more than compile and deploy:
- enforce branch and PR rules
- run security checks at the right stages
- generate evidence and reports
- stop critical risks while allowing safe progress
3) Vulnerability management that works in real teams
Scanning without process creates panic. DSOCP focuses on:
- severity handling and prioritization
- fixing vs accepting vs mitigating
- tracking work items and verifying fixes
- reducing repeated re-introductions
4) Secrets and identity hygiene
Many security incidents start with leaked credentials or weak identity controls. You learn:
- what not to store in repos
- how to handle secrets in pipelines
- how to reduce long-lived credentials
- how to avoid leaking secrets in logs and artifacts
5) Supply chain awareness
Modern apps depend on many packages, base images, and libraries. You learn:
- why dependency risk is real
- how to treat third-party code responsibly
- how to reduce exposure with versioning and policies
- why image hygiene matters
6) Security guardrails and policy discipline
Good guardrails create consistency:
- “must pass” checks
- “warn only” checks
- exception workflow for urgent releases
- policy rules that match business risk
Real-world projects you should be able to do after DSOCP
Below are expanded project outcomes. These are the kinds of deliverables that show real DevSecOps capability.
Project 1: Secure CI/CD pipeline with security gates
You should be able to build a pipeline that:
- runs tests and quality checks
- runs security checks at build time
- blocks release when critical risks exist
- stores reports as artifacts for traceability
- supports a controlled exception path (time-bound)
Why it matters: It turns security into a repeatable system instead of a meeting.
Project 2: Pull request security workflow
You should be able to enforce:
- code review checks
- protected branches
- required checks before merge
- security feedback on PR (clear, actionable output)
Why it matters: Fixing early is cheaper and faster.
Project 3: Dependency risk management workflow
You should be able to:
- detect vulnerable dependencies
- prioritize fixes by severity and exploitability
- update and test safely
- ensure issues do not come back repeatedly
Why it matters: Most teams inherit risk through dependencies.
Project 4: Container image hygiene and policy
You should be able to:
- choose secure base images
- reduce image size and attack surface
- scan images and enforce thresholds
- maintain version discipline and rollback safety
Why it matters: Containers multiply quickly; hygiene must be systematic.
Project 5: Secrets safe handling program
You should be able to:
- prevent secrets from entering git
- manage secrets centrally
- rotate credentials on schedule
- reduce hard-coded configs and hidden tokens
Why it matters: Credential leaks are one of the fastest ways to compromise systems.
Project 6: “Secure-by-default” pipeline templates
You should be able to create templates that:
- teams can reuse without redesigning everything
- include required security checks by default
- remain flexible for edge cases
Why it matters: Standardization is how you scale DevSecOps.
DSOCP mini-sections
What it is
DSOCP is a professional DevSecOps program that teaches you how to integrate security into the DevOps lifecycle using practical workflows, automation, and guardrails. The focus is secure delivery, not security theory only.
Who should take it
- Engineers building and releasing software to production
- DevOps/Platform engineers owning pipelines and deployment platforms
- Security engineers supporting engineering workflows
- SRE teams responsible for reliability outcomes
- Engineering managers driving secure delivery standards
Skills you’ll gain
- Building security into CI/CD with clear gates and thresholds
- Practical vulnerability lifecycle: detect, prioritize, fix, verify
- Secrets hygiene: storage, rotation, safe pipeline handling
- Secure release habits: approvals, evidence, audit-friendly flows
- Basic supply-chain thinking: dependencies and image hygiene
- Security guardrails as standards: policy mindset, exceptions, and alignment
Real-world projects you should be able to do after it
- A secure CI/CD pipeline with staged security checks and release rules
- A PR workflow that enforces security feedback before merge
- A dependency upgrade and vulnerability fix process that teams can follow
- A container image policy and scanning workflow with thresholds
- A secrets handling approach that prevents leaks and supports rotation
- A reusable secure pipeline template for multiple teams
Preparation plan
7–14 days (fast track, high intensity)
This works if you already do DevOps and want DevSecOps structure.
- Days 1–2: DevOps flow + where security fits (SDLC and CI/CD stages)
- Days 3–4: Core vulnerability types and how they appear in real logs
- Days 5–7: Secure CI/CD gates (what blocks, what warns, what is allowed)
- Days 8–10: Secrets discipline and safe configuration habits
- Days 11–12: Container and dependency hygiene basics
- Days 13–14: Build one full end-to-end secure pipeline project and document it
Key output: one project you can explain clearly in interviews.
30 days (balanced for working professionals)
This is the most realistic path for busy engineers.
- Week 1: DevSecOps mindset + threat basics + secure SDLC mapping
- Week 2: Secure pipeline design + PR workflow + reporting evidence
- Week 3: Dependency + container hygiene + secrets discipline
- Week 4: Capstone project + troubleshooting + revision through scenarios
Key output: secure templates + a repeatable checklist.
60 days (career shift or deeper confidence)
This is best if you are coming from dev-only, ops-only, or security-only.
- Weeks 1–2: Foundation (Git, CI/CD, Linux basics, cloud basics)
- Weeks 3–4: Security fundamentals and vulnerability lifecycle habits
- Weeks 5–6: DevSecOps implementation in pipelines and environments
- Weeks 7–8: Two projects + interview readiness + incident-style scenarios
Key output: multiple projects, strong system thinking, better interviews.
Common mistakes
- Tool-first thinking: teams add tools before deciding goals and rules, causing noise.
- Everything blocks releases: strict blocking rules without prioritization slow delivery and create bypass behavior.
- No clear severity policy: if everything is “critical,” teams stop trusting the process.
- Secrets treated casually: tokens in repos, CI variables exposed in logs, or long-lived keys never rotated.
- No exception process: real releases sometimes need exceptions; without a safe process, teams bypass controls.
- No ownership model: issues appear in reports but nobody owns fixing them.
- No verification loop: fixes are applied but never validated, so issues return.
Best next certification after this
A good next step depends on your direction:
- If you want broader end-to-end engineering delivery depth, move toward the integrated DevOps + DevSecOps + SRE learning ecosystem described in the MDE track page.
- If you want reliability outcomes and operational excellence, choose a reliability-focused learning route next.
- If you want leadership readiness, move toward management and governance skills where you define standards and outcomes.
Certification table
| Certification | Track | Level | Who it’s for | Prerequisites | Skills covered | Recommended order |
|---|---|---|---|---|---|---|
| DevOps Foundation | DevOps | Foundation | New engineers, developers moving into delivery | None | DevOps concepts, CI/CD basics | 1 |
| DevOps Professional | DevOps | Intermediate | DevOps engineers owning pipelines | DevOps basics | CI/CD workflows, automation habits | 2 |
| DevSecOps Certified Professional (DSOCP) | DevSecOps | Professional | DevOps, security, platform, SRE teams | DevOps basics recommended | Secure SDLC, secure pipelines, guardrails | 3 |
| SRE Professional | SRE | Professional | SRE and reliability owners | Ops exposure helps | SLO mindset, incident habits, reliability | 3 |
| AIOps / MLOps Path | AIOps/MLOps | Professional | Teams using automation and ML for ops | Monitoring basics | signals, automation, ML-ops habits | After core DevOps/SRE |
| DataOps Path | DataOps | Professional | Data engineers managing data delivery | Data pipeline basics | data delivery discipline, testing, automation | After core DevOps |
| FinOps Path | FinOps | Professional | Cloud cost and accountability owners | Cloud basics | cost governance, visibility, ownership | After cloud basics |
| Master in DevOps Engineering (MDE) | Integrated | Advanced | People wanting integrated DevOps + DevSecOps + SRE | No prerequisites stated on the page | DevOps/DevSecOps/SRE concepts + projects | After fundamentals |
Choose your path (6 learning paths)
Path 1: DevOps
Best for: engineers who want strong delivery automation and platform fundamentals.
Focus: pipeline ownership, deployment discipline, automation habits.
Typical outcomes you should aim for:
- stable CI/CD pipelines with clear stages
- repeatable release process
- basic infrastructure automation discipline
Best when you work in: product delivery teams, platform teams, internal tooling teams.
Path 2: DevSecOps
Best for: engineers who want secure delivery ownership.
Focus: security automation in CI/CD, secure configs, safe dependencies.
Typical outcomes you should aim for:
- security gates that are practical
- secrets discipline across teams
- reduced vulnerability backlog and fewer late fixes
Best when you work in: fintech, SaaS, regulated environments, cloud-native platforms.
Path 3: SRE
Best for: engineers who own uptime and reliability outcomes.
Focus: safe change management, incident response discipline, observability-first thinking.
Typical outcomes you should aim for:
- fewer production incidents caused by changes
- measurable reliability improvements
- better runbooks and post-incident prevention
The official MDE agenda includes learning SRE concepts and practices as part of the integrated program.
Path 4: AIOps / MLOps
Best for: engineers who want automation at scale and smarter operations.
Focus: signals, noise reduction, automation, and ML-in-production thinking.
Typical outcomes you should aim for:
- cleaner alerting and better incident detection
- automation of repeated operational work
- pipelines and governance for ML models (if MLOps)
Path 5: DataOps
Best for: data engineers and analytics platform teams.
Focus: reliable data delivery, testing habits, automation, and governance.
Typical outcomes you should aim for:
- fewer broken pipelines
- predictable data releases
- measurable quality and freshness checks
Path 6: FinOps
Best for: cloud cost owners, platform leads, and managers running cloud accountability.
Focus: visibility, ownership, policy, and cost discipline.
Typical outcomes you should aim for:
- clean tagging and ownership mapping
- budget and usage accountability
- cost guardrails integrated into engineering workflows
Role → recommended certifications mapping
| Role | What the role is measured on | Recommended certification focus | Why it fits |
|---|---|---|---|
| DevOps Engineer | delivery speed + stability | DevOps + DSOCP | You own pipelines; DevSecOps makes them safer |
| SRE | reliability outcomes | SRE + DevSecOps basics | Secure changes reduce incidents and rollback risk |
| Platform Engineer | platform standards + reusability | DevOps + DSOCP + standardization | Secure-by-default templates scale across teams |
| Cloud Engineer | cloud configs + access | DevOps + security guardrails | Cloud misconfig is a major risk area |
| Security Engineer | risk reduction + controls | DSOCP | Helps you push controls into developer workflows |
| Data Engineer | pipeline reliability + data quality | DataOps + DevSecOps basics | Data security and governance are real delivery concerns |
| FinOps Practitioner | cost ownership + visibility | FinOps + delivery awareness | Cost is now an engineering outcome, not only finance |
| Engineering Manager | outcomes + risk + adoption | leadership + DevSecOps understanding | You need standards that reduce risk without slowing teams |
Next certifications to take (3 options)
Option 1: Same track (deeper DevSecOps)
Choose this if: your main job is secure delivery and governance in pipelines.
Why: you can go deeper into policies, secure templates, and stronger supply-chain discipline.
Option 2: Cross-track (DevSecOps + Reliability)
Choose this if: you own production systems and uptime outcomes.
Why: secure delivery and reliable delivery work best together. Reliability practices make security changes safer and smoother.
Option 3: Leadership path
Choose this if: you lead teams or programs.
Why: you will need adoption strategy, governance, and measurement, not only tools.
List of top institutions providing training + certification support
DevOpsSchool
DevOpsSchool provides structured training paths across DevOps, DevSecOps, and SRE learning areas. It is useful for engineers who want a guided roadmap and project-driven learning that matches real delivery work. It also helps teams standardize skills through repeatable learning plans.
Cotocus
Cotocus is positioned as a supporting brand in the DevOps learning ecosystem. It is helpful for learners who want practical exposure aligned to real delivery, automation, and platform problems. It can also be useful for teams that want a structured skill-building approach.
ScmGalaxy
ScmGalaxy supports structured learning in DevOps and related areas. It is useful for learners who prefer step-by-step progression and practice-led improvement. It can also help teams that want to build consistent operational habits.
BestDevOps
BestDevOps is positioned as a knowledge and community brand for DevOps professionals. It can help learners understand role expectations, skill direction, and practical career awareness. It supports continuous learning and skill mapping.
DevSecOpsSchool
DevSecOpsSchool focuses on DevSecOps learning themes and secure delivery thinking. It is useful when you want security-first pipeline knowledge and structured coverage of secure delivery practices. It supports professionals moving from DevOps into DevSecOps.
SREschool
SREschool focuses on reliability engineering outcomes like safe change, uptime, and incident learning. It is helpful for SREs and platform teams that own reliability in production. It complements DevSecOps because secure systems must also stay reliable.
AIOpsSchool
AIOpsSchool aligns learning around automation, signals, and AI-assisted operations. It is useful for teams dealing with alert fatigue and repeated operational incidents. It fits well after you build a strong base in DevOps and observability habits.
DataOpsSchool
DataOpsSchool supports data teams that want consistent delivery for data pipelines. It is helpful for collaboration across data, platform, and governance teams. It encourages repeatable process thinking, similar to DevOps, but for data workflows.
FinOpsSchool
FinOpsSchool supports cost accountability and cloud governance thinking. It is useful for engineers and managers who want cost visibility, ownership models, and guardrails that scale. It helps connect technical decisions with business cost outcomes.
FAQs focused on difficulty, time, prerequisites, sequence, value, outcomes
1) Is DSOCP difficult for a beginner?
It can be challenging if you are brand new to CI/CD and cloud basics. If you are new, the best approach is to first understand the delivery flow (build, test, deploy) and then add security into it step by step.
2) How much time does DSOCP preparation usually take?
If you already work with DevOps pipelines, 30 days is realistic. If you are switching roles, 60 days is safer because you need time to build foundation plus projects.
3) What prerequisites should I have?
Basic Git, basic CI/CD understanding, and comfort with reading logs are very helpful. If you lack these, start with a foundation plan first, then move into DevSecOps.
4) What is the right sequence: DevOps first or DevSecOps first?
DevOps first is usually better for complete beginners, because DevSecOps is “security inside DevOps.” If you don’t know the pipeline, it becomes harder to secure it.
5) Is DSOCP valuable for software engineers who do not deploy?
Yes, because modern developers still influence runtime risk through dependencies, configs, secrets handling, and code patterns. DSOCP helps you write changes that are safer to ship.
6) What career outcomes does DSOCP support?
It supports roles like DevSecOps engineer, security-focused DevOps/platform engineer, secure CI/CD owner, and security automation engineer. It also strengthens promotion readiness for engineers who can own end-to-end delivery risk.
7) Does DSOCP help in interviews?
Yes, if you can explain your project work clearly: where security gates sit, what they enforce, and how you handle exceptions. Interviewers care about implementation thinking, not only tool names.
8) Will DevSecOps slow down delivery?
Bad DevSecOps slows delivery because it blocks everything and creates noise. Good DevSecOps speeds delivery because it prevents rework, reduces hotfixes, and improves release confidence.
9) How do I avoid “scan noise” in DevSecOps?
Set clear thresholds (what blocks vs what warns), and focus on critical issues first. Keep reports actionable and avoid flooding teams with low-value alerts.
10) What should I build to prove skills after DSOCP?
Build at least one secure CI/CD pipeline project with PR checks, scanning, secrets hygiene, and clear release rules. Add a short write-up that explains your decisions.
11) What is a common reason people fail to implement DevSecOps?
They treat it as tool installation instead of a workflow change. Without clear policies and ownership, tools generate reports but do not reduce risk.
12) What is the best next step after DSOCP?
Choose one based on your role: deepen secure delivery (same track), add reliability skills (cross-track), or move into leadership and governance practices (leadership path).
FAQs specifically on DSOCP
Q1) What does DSOCP “certify” in practical terms?
It certifies your ability to apply DevSecOps principles in real delivery workflows: secure pipeline stages, guardrails, vulnerability handling, and safe configuration habits.
Q2) What should I be able to explain after DSOCP?
You should be able to explain: where security fits in the SDLC, what checks run in CI/CD, how you decide blocking rules, and how you handle exceptions safely.
Q3) What is the most important mindset to succeed with DSOCP?
Think “secure-by-default and automate what repeats.” If a safe step is repeated, it should be part of the pipeline template.
Q4) What is the best project style for DSOCP learning?
A realistic project is better than a toy project. Use a service that has dependencies, builds a container, deploys, and produces logs. That creates real security surfaces.
Q5) How should I handle vulnerabilities I cannot fix quickly?
Use a clear workflow: classify severity, decide fix vs mitigate vs exception, document ownership, and set a timeline. Avoid ignoring issues with no plan.
Q6) How do I show business value from DSOCP skills?
Show reduced late-stage fixes, fewer emergency patches, fewer incidents caused by risky changes, and faster approvals because evidence is automated.
Q7) What is the biggest DevSecOps mistake in CI/CD?
Blocking everything without prioritization. That creates bypass behavior and destroys trust. Practical thresholds build trust and real adoption.
Q8) What is the best revision method before assessment?
Revise using scenarios: “critical vulnerability found before release,” “secret leaked,” “unsafe dependency update,” “risky configuration change.” Practice your decision flow and pipeline controls.
Conclusion
DSOCP is most valuable when you treat it as a delivery upgrade, not a security side-task. The real outcome is simple: teams ship faster with fewer risky changes, fewer late fixes, and fewer avoidable incidents. Focus on building secure pipelines, standard templates, clear severity rules, and strong secrets hygiene. That is what turns DevSecOps into a career advantage and a real business win.